Passwordless authentication, also known as passwordless MFA, is a type of MFA that verifies user identity without relying on passwords or other memorized secrets. While most forms of passwordless authentication are multi-factor (MFA), simpler forms exist such as email-delivered magic links.
Instead of using passwords, identity can be verified based on a “possession factor.” For example, possession of an object that uniquely identifies the user because no other user would be expected to have the object (e.g. a registered mobile device or an issued hardware token). In passwordless, identity can also be confirmed using “inherent factors” such as a person’s biometric signature (e.g. fingerprint, voice, face or retinal scan).
The landscape for passwordless authentication can be divided into two distinct solution types: CIAM or consumer identity and access management, and WIAM or workforce identity and access management. While both types of solutions may be purchased by “enterprises” or organizations, but the workforce IAM refers to a passwordless solution used by employees of an organization to access a myriad of resources and IT services, while CIAM refers to a passwordless solution used by the organization’s customers (generally accessing resources over the public Internet).
Why is it needed?
Since the dawn of computing, the de facto approach for user authentication has been the password. The problem with this is that unlike possession or inherent factors, an authentication method that is based on a shared secret, ie. something the user knows (such as a password, passphrase, or PIN code) is generally stored in a centralized database. This makes the secret susceptible to theft (either by attacking the shared secret database or socially engineering an attack to have the user share the password). Users are human and engage in risky behavior such as reusing passwords, choosing easy to guess passwords or even sharing and writing down their passwords in places where others can see it. As a result, passwords are one of the biggest cyberattack vectors and have been responsible for 81% of breaches. They also lead to attacks such as credential stuffing, corporate account takeover (CATO), password spraying and brute force attacks.
While we won’t go into all the problems with passwords, suffice it to say that passwords also create more negative user authentication experiences and create significant management costs for IT operations and help desks as users are locked out of their accounts.
Benefits of Passwordless Authentication
Passwordless authentication offers numerous benefits at both a business and technical level.
Business:
- Better security: Passwordless eliminates the target of phishing attacks and invalidates all the compromised credentials that exist on the Dark Web. This slashes the attack surface area that organizations must protect.
- User Experience (UX): Passwordless offers a more streamlined and universal interface for authentication that is less onerous on the user.
- Lowers costs / increases ROI: Passwords require constant maintenance from your IT staff. Removing them reduces support tickets and frees IT to deal with other problems, all while contributing to your ROI.
Technical:
- Decentralized: Because passwordless doesn’t require a master list of passwords or a password manager, it’s decentralized, meaning a breach doesn’t compromise the security of your entire system.
- Passwordless generally requires no extra object to carry around since most solutions leverage the ubiquity of user smart phones (an exception being a FIDO security key).
- Broad standards-based support – In addition to supporting industry-wide standards like SAML and OAUTH, modern passwordless solutions are FIDO2-compliant and support improved authentication user flows such as synchronized passkeys or device-bound passkeys (formerly called security keys).
How Does Passwordless Authentication Work?
There are three types of factors that can be used in an MFA solution – something you are (biometric authentication), something you know (password), or something you have (mobile device). The one factor that is often changed from 2FA and MFA is the weakest factor of the three; namely, ‘something you know,’ such as a password.
Nearly all passwordless MFA solutions stipulate a factor based on ‘something you own or have.’ To further strengthen authentication, many add or substitute ‘something you are,’ typically verified with biometrics.
One framework that guides most passwordless authentication solution architectures comes from the FIDO standard, a broadly accepted industry standard that specifies a highly secure interchange of keys built on public key cryptography to authenticate users. For a deeper dive on FIDO, consult our Complete Guide to FIDO and related standards.
What Is the Difference Between Passwordless and traditional MFA?
Passwordless is a form of MFA, but why isn’t traditional MFA good enough? Whether it’s 2FA vs passwordless authentication or other MFA alternatives, prior MFA approaches have several downsides. Most importantly, traditional MFA is built on top of a password, so end users still have the recall problem we discussed before. Additionally, the 2nd factor typically adds user frustration to the picture with OTPs (one-time passcodes) that require extra typing. A solution to this is simply a mobile push confirmation, but recently even this factor has become susceptible to compromise through MFA push bombing. A passwordless login solves problems traditional MFA may cause (or at least not fix), from a choppy user experience and “MFA fatigue” to serious problems like compromised credentials showing up on the dark web.
Passwordless Authentication and Phishing-Resistant MFA
MFA also remains vulnerable to elaborate duplicitous “man in the middle” (MITM) attacks in which adversaries trick users into entering keys and OTPs into fake log-in pages so they can turn around and use them to access the real sites. So, for all the friction it causes with users, we can safely conclude that traditional MFA does not make us phishing-resistant.
The growing menace from these attacks as well as the Colonial Pipeline Attack which affected societal operations led to the Biden presidential administration passing memorandum 22-09 in early 2022, mandating that all critical infrastructure industries implement “phishing-resistant MFA” by 2024.
This complements guidance from NIST, CISA and other standards bodies that also detail MFA requirements and differing measures that can be taken to attain higher levels of security assurance.
The growing move to phishing-resistant MFA plays well with passwordless MFA or authentication, because most passwordless authentication solutions are phishing-resistant. So, in essence, most passwordless authentication supports the push to wider spread use of phishing-resistant MFA inherently. Click here for a more in-depth analysis of phishing-resistant MFA.
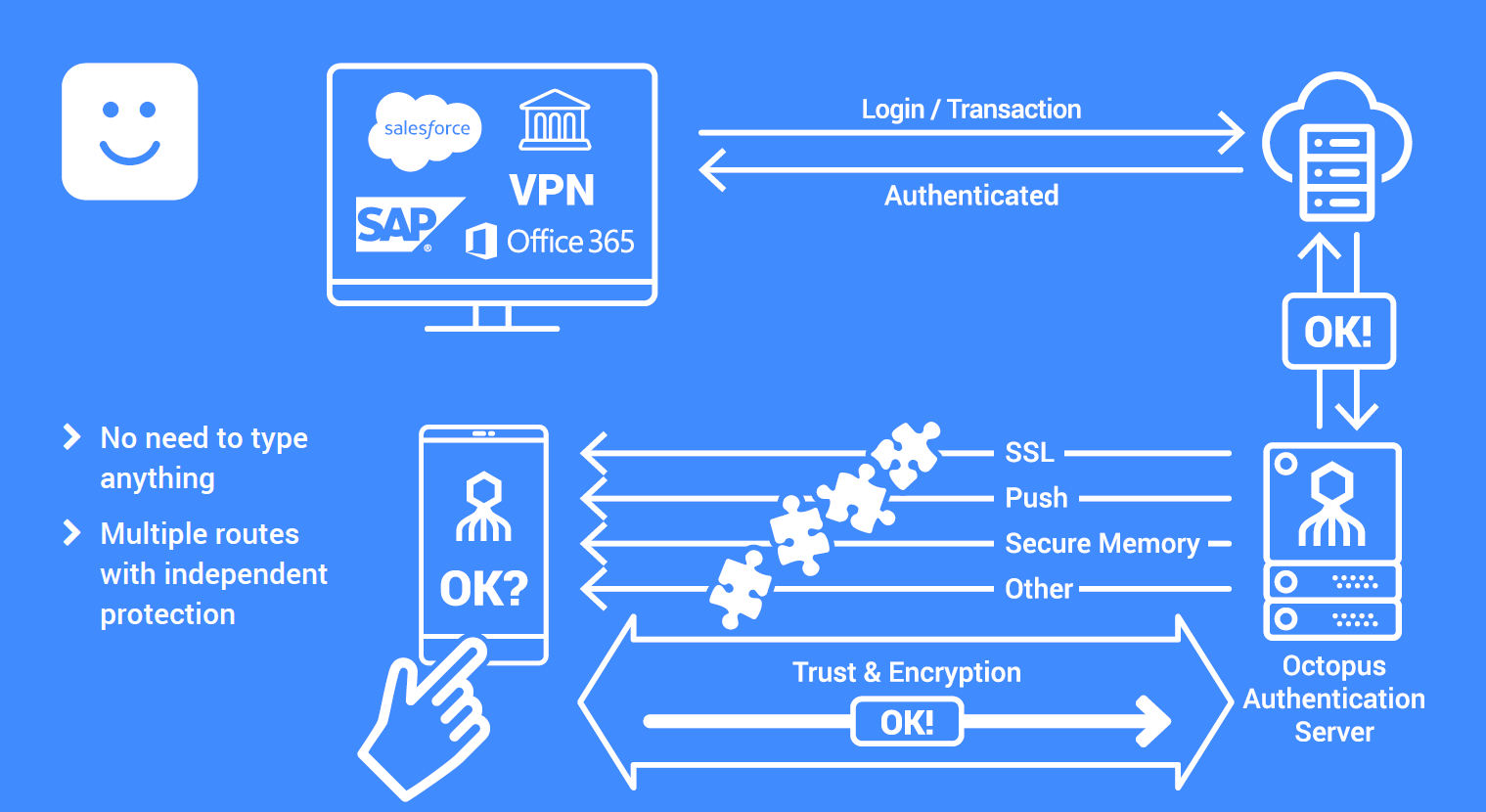
How Does Double Octopus Do Passwordless?
Secret Double Octopus is the industry leader for workforce Passwordless Authentication having won numerous awards for our proven enterprise-level solutions. More than 150K users authenticate securely with the Octopus platform daily.
Our Passwordless solution is a complete one, known as “full passwordless.” Some companies sell Passwordless solutions that are not fully Passwordless as they don’t offer coverage for onprem and legacy apps and desktop access.
The Octopus platform offers the broadest enterprise use case coverage and is ideal for industries such as higher education and critical infrastructure. Mandates from the Biden administration and other governments call for critical infrastructures and other industries to move toward Zero Trust security postures and phishing-resistant MFA.
Passwordless MFA represents the best approach for phishing-resistance but making the transition can be a big job. SDO offers the ability to slowly transition from password-based to Passwordless, with milestones along the way to becoming a fully Passwordless organization. We focus on adding Passwordless to your existing infrastructure, instead of forcing you to restructure to make our solution fit.


Learn more about passwordless authentication
The post Passwordless Authentication first appeared on Secret Double Octopus.
The post Passwordless Authentication appeared first on Secret Double Octopus.